All-Environment Web Application Firewall
Protect web applications, services, e-commerce shops and APIs from common web vulnerabilities and cyber threats. No matter whether you're hosting on-premises, in the cloud or in hybrid environments.
Protect web applications, services, e-commerce shops and APIs from common web vulnerabilities and cyber threats. No matter whether you're hosting on-premises, in the cloud or in hybrid environments.
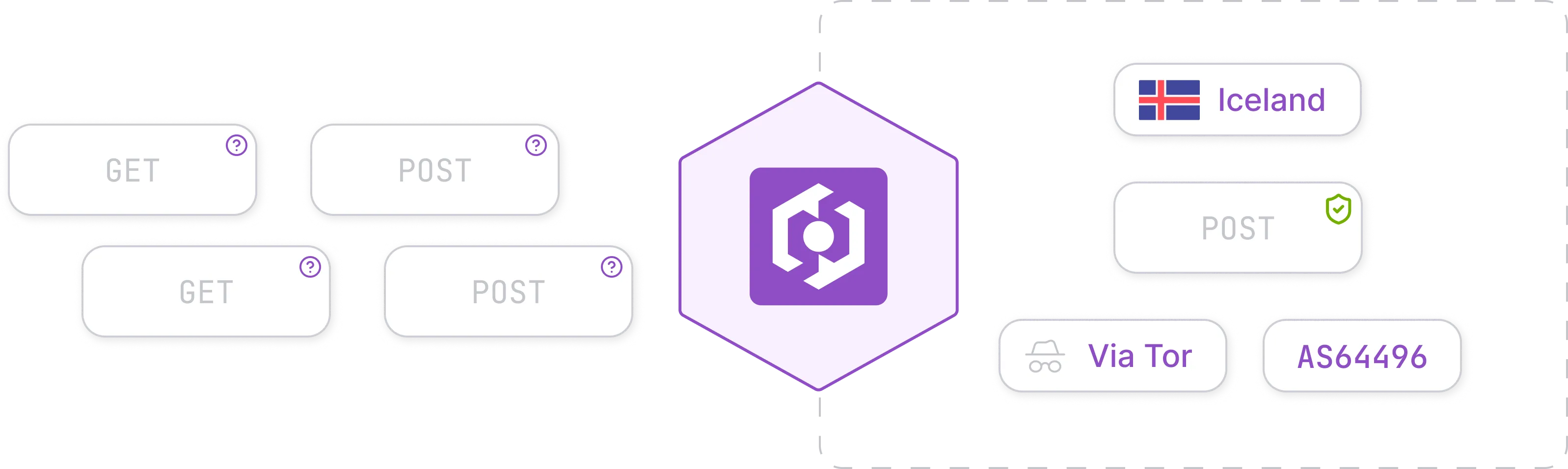
Purpose-Built For All Environments
Our WAF solution comes with a variety of flexible features allowing it to be used in nearly any environment with any workload imaginable.
Tailored Protection
Extensible rulesets and flexible configuration options make it easy to adapt rescaled WAF to your specific workload and security needs.
- id: gen-ssrf-003
name: Cloud Metadata SSRF (AWS)
expression: |
string(query).contains("169.254.169.254") ||
string(body).contains("169.254.169.254") ||
string(query).contains("/latest/meta-data")
score: 100
enabled: true
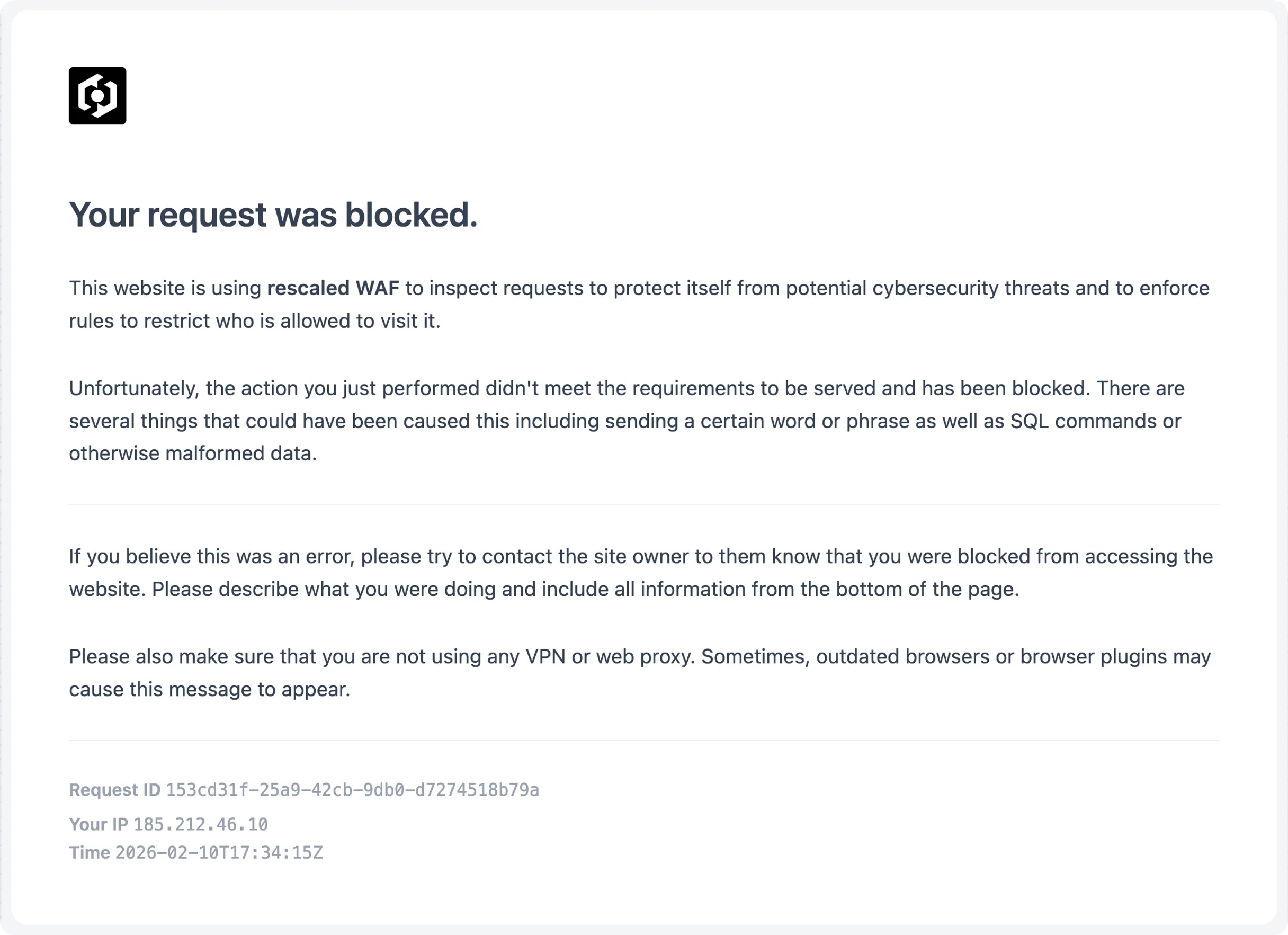
Smart Blocklisting
Every request is being analyzed and prepared by out threat intelligence engine to allow for smart blocking rules based on extended fields that go beyond the scope of the HTTP protocol.
Block Cyberthreats At The Edge
Setting up a Web Application Firewall (WAF) doesn't make magically immune against cyber attacks. But it helps you to reduce exposure to common threats and to make it harder for threat actors to exploit your applications.
Request pricing or schedule a technical demo for your engineering team.
We're happy to get in contact with you!